
Archive for 2012
Crocker inducted into Internet Hall of Fame
Posted by Mark Feldman in Uncategorized on May 1, 2012
Steve Crocker, ICANN board chairmen and DNSSEC Deployment Initiative member, was inducted into the Internet Society’s Internet Hall of Fame as an Internet Pioneer.
Steve was honored for a lifetime of Internet accomplishments, including starting the RFC series. He talked about the RFCs and the openness of Internet protocols several years ago in his New York Times Op Ed, How the Internet Got Its Rules, on the 40th anniversary of the publication of RFC 1.
Steve continues to push for improvement of Internet infrastructure security, including the deployment of DNSSEC and the adoption of BCP 38.
Call for Participation — ICANN DNSSEC Workshop 27 June 2012
Posted by Mark Feldman in Uncategorized on April 26, 2012
As seen on the DNSSEC Deployment Working Group mailing list:
The DNSSEC Deployment Initiative, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), is planning a DNSSEC Workshop at the ICANN meeting in Prague, Czech Republic on 27 June 2012. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN Costa Rica meeting on 14 March 2012. The presentations and transcripts of the presentations are available at http://costarica43.icann.org/node/29659.
We are seeking presentations on the following topics:
1. DNSSEC activities in Europe
This is a key panel and we are seeking participation from those who have been involved in DNSSEC deployment in Europe as well as those who have a keen interest in the challenges and benefits of deployment. Key questions are to consider include: what would help to promote DNSSEC deployment? What are the challenges you have faced when you deployed DNSSEC? Can DNSSEC make the information users receive more reliable?
2. ISPs and Validation
ISPs are beginning to take the first step to full DNSSEC implementation that will allow web users, with software applications like browsers, to validate that the destination they are trying to reach is authentic and not a spoofed website. We are seeking ISPs to participate in a panel discussion or provide presentations on their DNSSEC deployment plans, challenges, and benefits for users.
3. The realities of running DNSSEC
Now that DNSSEC has become an operational norm for many registries and registrars, what have we learned about how we manage DNSSEC? What’s best practice around key rollovers? How often do you review your disaster recovery procedures? Is there operational familiarity within your customer support teams? Has DNSSEC made DNS more ‘brittle’ or is it just a run-of-the-mill operational practice?
4. DNSSEC and Enterprise Activities
DNSSEC has always been seen as a huge benefit to organizations looking to protect their identity and security on the Web. Large enterprises are an obvious target for DNS hackers and DNSSEC provides an ideal solution to this challenge. This session aims to look at the benefits and challenges of deploying DNSSEC for major enterprises. Topics for discussion:
What is the current status of DNSSEC deployment among enterprises?
What plans do the major enterprises have for their DNSSEC roadmaps?
What are the challenges to deployment for these organizations? Do they foresee raising awareness of DNSSEC with their customers?
5. When unexpected DNSSEC events occur
What have we learned from some of the operational outages that we have seen over the past 18 months? Are there lessons that we can pass on to those just about to implement DNSSEC? How do you manage dissemination of information about the outage? What have you learned about communications planning? Do you have a route to ISPs and registrars? How do you liaise with your CERT community?
6. DNSSEC in the wild
What operational statistics have we gathered about DNSSEC? Is it changing DNS patterns? How are our nameservers handling DNSSEC traffic? Is the volume as expected? Have we seen anything unusual? Are there experiences being documented in the form of best practices, or something similar, for transfer of signed zones?
7. DANE and other DNSSEC applications
Using DNSSEC as a means of authentication for http transactions is an exciting development of DNSSEC. What is the progress of the DNS-Based Authentication of Named Entities (DANE) initiative? (See http://datatracker.ietf.org/wg/dane/.) How soon could DANE become a deployable reality and what will be the impact of such a deployment, e.g. impact on traditional certification authorities (CAs)?
8. The Great DNSSEC Panel Quiz
Ever fancied pitting your wits against your colleagues? Demonstrate your knowledge and expertise in DNSSEC in our Great DNSSEC Panel Quiz. We are looking for four or five people to join us in a light-hearted quiz.
In addition, we welcome suggestions for additional topics. If you are interested in participating, please send a brief (1-2 sentence) description of your proposed presentation. Here are the relevant deadlines:
10 May 2012 — Deadline to submit brief description of presentation from interested participants
04 June 2012 — Deadline to submit presentation slides
Please respond to [email protected] no later than 10 May 2012 as indicated above. We hope that you can join us.
Thank you,
Julie Hedlund
On behalf of the DNSSEC Workshop Program Committee:
Luis Diego Espinoza, NIC .cr
Steve Crocker, Shinkuro
Simon McCalla, Director of IT, Nominet UK
Russ Mundy, Cobham
Ondřej Surý, NIC.cz
Lance Wolak, Vice President, Marketing & Sales, .ORG, The Public Interest Registry
SIDN’s excellent DNSSEC tutorial
Posted by Mark Feldman in Uncategorized on April 23, 2012
We agree with our friends at the ISOC Deploy360 Programme when they say that the e-learning course on DNSSEC from SIDN, the .NL registry, is excellent.
Leveraging DNSSEC to protect BGP
Posted by Mark Feldman in Uncategorized on April 23, 2012
It’s not news to anyone involved in the deployment of DNSSEC, but some of the Internet protocols we use today were designed years ago, when the Internet itself was as much a research project as the research projects it helped facilitate at university and government or government-funded institutions. Many of the insecure protocols of those days have been replaced or augmented by more secure versions. Telnet and rlogin/rsh have given way to ssh. There’s now HTTPS in addition to HTTP and many other protocols now support end-to-end security using SSL/TLS.
Even with all of these changes to transport and application-level security, infrastructure security has lagged behind. DNSSEC is one piece of the puzzle to secure the infrastructure. It ensures that the mappings that DNS provides — that are required by just about every other protocol and application on the Internet — are the ones intended by domain owners.
But even having validating mappings that result in, among other things, IP addresses is insufficient. Another piece of infrastructure — this one far more hidden from end users than DNS — is routing. Specifically, it’s the Border Gateway Protocol (BGP) that is used to identify how packets should flow between corporate and ISP networks across the Internet to get to their intended recipients.
BGP has been under study to improve its security for as long as DNS. Many of the same organizations that have funded or performed work on improving DNS security have done the same for BGP. The US Department of Homeland Security, which funds the DNSSEC Deployment Initiative, has also funded work on securing BGP.
As reported in The Register, those securing BGP are benefiting from the deployment of DNSSEC with the development of BGP Route Origin Verification (ROVER). According to the article,
Several early adopter telcos and ISPs are in the process of publishing route origins in their reverse DNS and signing with DNSSEC. In addition, Secure64 has established a Rover Testbed available at “rover.secure64.com” (registration required).
This adds BGP to the growing list of protocols and services that can benefit from leveraging DNSSEC deployment.
Ukraine signed ahead of schedule
Posted by Mark Feldman in Uncategorized on April 17, 2012
As reported previously, the .UA hostmaster provided a schedule for DNSSEC deployment at ICANN43.
In a comment this past Friday on that article and in a press release on their own site, the .UA hostmaster announced that they’re signed, their DS is in the root, and several companies are already using DNSSEC to protect their domains. They end their press release with the following:
UA is our home, let’s make it safe!
FCC DNSSEC Recommendations for ISPs Published
Posted by Mark Feldman in Uncategorized on April 9, 2012
The recommendations that were previously announced have been published on the FCC’s CSRIC III website.
In brief, the report (318KB PDF) lays out four levels of possible deployment with respect to validation and recommends that all ISPs implement at least the next to highest level, DNSSEC-aware resolvers, if not the highest level, actual validation at the ISP level. This lays the foundation for ISPs to go to the next step and, perhaps more importantly, enables end systems to do their own validation without having to bypass the ISP’s DNS service completely.
Labs around the world enabling DNSSEC
Posted by Mark Feldman in Uncategorized on March 30, 2012
In addition to planning for DNSSEC and applying metrics, Government and TLD registry labs around the world are producing tools that enable the deployment of DNSSEC.
In the case of the ccTLDs, these same countries are leading in the adoption of DNSSEC. The rest of us benefit from their sharing their work. Following are some of the labs and what they provide.
CZ.NIC Labs (ICANN 44 is being hosted by CZ.NIC):
- DNSSEC Hardware Tester
- DNSSEC Validator Extension for Web Browsers
- Knot Authoritative DNS Server
- Unbound validating recursive and caching DNS resolver
- Dnssec-Trigger local Unbound server for end-system validation
- NSD authoritative only, high performance, simple and open source name server
- DNS Check DNS server checking and error reporting
- DNSViz DNS visualization tool
US DHS S&T Cyber Securtity R&D-funded:
- DNSSEC Debugger DNSSEC analyzer
FCC recommendations promote DNSSEC capability
Posted by Mark Feldman in Uncategorized on March 22, 2012
The US Federal Communications Commission‘s Communications Security, Reliability, and Interoperability Council (CSRIC) has come out with recommendations to ensure that end-users’ ability to use DNSSEC is not impaired by ISP infrastructure. The report is not yet out, but there is a fact sheet and a press release that states:
DNS Best Practices:
CSRIC recommended that ISPs implement best practices to better secure the Domain Name System. DNS works like a telephone book for the Internet, but lack of security for DNS has enabled spoofing, allowing Internet criminals to coax credit card numbers and personal data from users who do not realize they are on an illegitimate website. DNSSEC is a set of secure protocol extensions that prevent such fraudulent activity. This recommendation is a significant first step toward full DNSSEC implementation by ISPs and will allow users, with software applications like browsers, to validate that the destination they are trying to reach is authentic and not a spoofed website.
The slide presentation (2.7MB pptx) on DNSSEC from today’s meeting is available from the CSRIC III web site, as are FCC chairman Genachowski’s remarks. A video of the meeting is also on the FCC’s web site.
Is a $70 router fast enough for DNSSEC?
Posted by Olafur Gudmundsson in Adoption, Case Studies, DNSSEC on March 22, 2012
In a blog post a few days ago, Bob Novas talked about configuring an inexpensive home router as a DNSSEC validator for a home/small office network.
Such a router has much less computational power than most computers today, so many people assume it is not fast enough to do DNSSEC validation. To test that assumption, I ran the router through a set of tests designed to measure DNS and DNSSEC validation performance. I ran each of the following tests in sequence against the router with DNSMASQ (the default, non-validating forwarding resolver used by OpenWrt), Unbound without validation, and Unbound with validation:
- Test #1 Cold cache: query for X signed names from 2 different zones
- Test #2 Warm cache: query once for each of the names in #1
- Test #3 Mixed case query for the names in cache and intermingle 30% queries for names not in cache
- Test #4 Remote Ask for 50 nonexistent names in .gov
In tests 1-3, the names queried are from zones served by authoritative servers on the same LAN, minimizing network delays.
The reason I have the value X above is that I use different values depending on the speed of the device under test. The goal of the tests is to run experiments #1 and #3 for just long enough to get meaningful results.
When running without DNSSEC, DNSMASQ and Unbound performed about the same In the Cold test — around 700 queries/second.
Unbound was six times faster on the Warm test since it caches responses and DNSMASQ doesn’t. Unbound was two faster on Mixed test for the same reason.
With DNSSEC turned on, Unbound was able to handle about 140 validated queries/second, which is quite fast. This is with answers that are signed by a 1024-bit RSA key. It ran at the same speed as it did without DNSSEC in the Warm case.
This performance is more than enough for a home or small office.
When comparing the results for the Remote test, validating Unbound finished in about seven seconds while non-validating DNSMASQ took about ten. Network delay, not validation time, dominates the time to perform this test. In non-test situation, DNSSEC validation thus will not be a bottleneck when the doing lookups from the Internet.
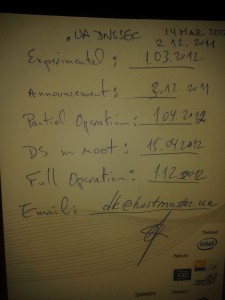
Menu for .UA DNSSEC deployment
Posted by Mark Feldman in Uncategorized on March 19, 2012
At ICANN43, Steve Crocker, ICANN Board Chairman and DNSSEC Deployment Initiative memember, met with Dmitry Kohmanyuk, the .UA hostmaster. On the back of a menu for the Gala Dinner, Dmitry outlined the plans for .UA DNSSEC deployment.
Crocker notes
This makes the set of DNSSEC deployment maps I presented on the 14th obsolete, and I’m very happy about that.
Planned .UA DNSSEC a of 14 March 2012
(As with other menus, substitutions may occur)
- Experimental: 1 March 2012
- Announcement: 3 December 2011
- Partial Operation: 1 April 2012
- DS in Root: 15 April 2012
- Full Operation: 1 December 2012





Recent Comments